What is sensitive data? Understanding its importance and protection strategies

Every time you log into a bank account, upload medical records, or file taxes online, you share sensitive data. If this data is exposed, it could lead to identity theft, financial harm, or reputational damage. That's why protecting it is essential to data privacy and data security.
In this article, we examine different types of sensitive data, explain how data sensitivity is measured, and provide practical steps individuals and organizations can take to protect it.
Note: This information is for general educational purposes and not legal advice.
Introduction to sensitive data
Sensitive data is generally defined as any information that, if exposed or misused, could result in harm to an individual or organization. Examples range from health records, financial account details, and login credentials to trade secrets, proprietary business information, and government-classified materials.
Sensitive data vs. personal data
In casual conversation, the terms "sensitive data" and "personal data" may sometimes be conflated. However, they’re not always the same thing.
Personal data is any information that identifies an individual or can be linked to an identifiable individual. It commonly refers to details like your name, email address, phone number, or date of birth.
Sensitive data generally refers to any information that could cause harm to an individual or organization if exposed. This includes certain types of personal data, such as financial account details, medical records, government identification numbers, and login credentials. But it can also include sensitive information that’s not personal data, such as trade secrets or government documents.
This distinction between sensitive data and personal data is important because regulations and privacy laws typically treat them differently. For example, the General Data Protection Regulation (GDPR) and Health Insurance Portability and Accountability Act (HIPAA) impose stricter requirements for handling data that falls under the above classification of sensitive data.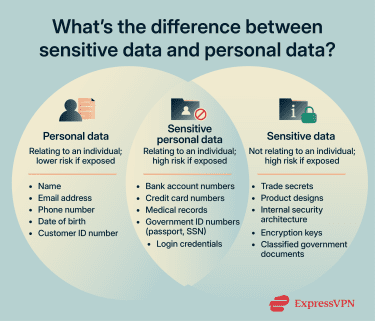
Two other related terms are “Personally Identifiable Information (PII)” and “personal information.”
PII is a term commonly used in U.S. regulations and privacy guidance that refers to any information that identifies or can be used to identify an individual. It includes both sensitive PII, which could cause harm if exposed, and non-sensitive PII, which is lower risk. In other words, PII overlaps with both sensitive data and personal data but is limited to information that relates to individuals.
Personal information is a term used in the California Consumer Privacy Act (CCPA) that’s essentially synonymous with PII, but is a slightly broader category that also includes household and device-level data.
Understanding the types of sensitive data
Sensitive data comes in many forms. Here are the main categories of sensitive data, what they include, and the risks associated with their exposure.
Financial information
Financial information includes bank account numbers, credit history, and investment records. It’s also payment card data such as credit or debit card numbers, cardholder names, expiration dates, and CVV codes. This information is considered sensitive because exposure can enable fraud, unauthorized transactions, or identity theft.
Protected health information
Protected health information (PHI) encompasses medical records, treatment histories, diagnostic results, and related health data. PHI is sensitive because disclosure can lead to privacy violations, discrimination in employment or insurance, and medical identity theft.
Access credentials and authentication data
This includes usernames, passwords, PINs, security questions, two-factor authentication (2FA) or multi-factor authentication (MFA) tokens, and other credentials used to access accounts. It’s sensitive because compromised credentials can provide attackers with unauthorized access to financial accounts, corporate systems, or personal devices.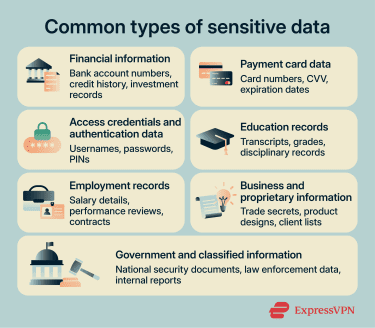
Education records
Education records include transcripts, grades, disciplinary records, and other academic information tied to a student. These records are sensitive because they contain personal and academic history. They could be misused to harm a student’s reputation, facilitate identity theft, or enable discrimination in future employment or educational opportunities.
Employment records
Employment records cover salary details, performance reviews, employment contracts, benefits, and disciplinary actions. These are sensitive because disclosure can damage professional reputation, enable workplace discrimination, or be used in employment identity theft schemes.
Business and proprietary information
Business and proprietary information includes trade secrets, business plans, product designs, client lists, and internal strategies. This data is sensitive because its exposure can compromise competitive advantage, result in financial losses, or trigger legal disputes.
Government and classified information
Government and classified information include documents and data related to national security, law enforcement, or internal government operations. This information is sensitive because unauthorized disclosure can endanger public safety, national security, or government operations.
The importance of protecting sensitive data
Protecting sensitive data is important because exposure can have serious consequences for both individuals and organizations.
Personal risks
For individuals, compromised sensitive data can lead to:
- Identity theft: Credit accounts, loans, or large purchases could be carried out in the victim’s name, potentially damaging credit scores and creating long-term financial challenges.
- Unauthorized access to accounts: Control over bank, email, social media, or other personal accounts could lead to financial loss, data exposure, or impersonation.
- Fraudulent filings: Tax returns, credit applications, or government benefit claims can be made using stolen information.
- Discrimination: Exposure of sensitive details such as health status, disability, or other personal characteristics can influence employment decisions, insurance eligibility, or lending outcomes.
- Damage to reputation: Leaked personal or professional details such as private emails, photos, or performance reviews can harm relationships, career prospects, or social standing.
- Privacy violations: Disclosure of communication information (like phone numbers), precise location data, or medical records can potentially lead to doxxing, harassment, unwanted tracking, or exploitation.
Organizational risks
For organizations, failing to safeguard sensitive data can lead to:
- Financial losses: Cyberattacks, ransomware, or corporate espionage can result in direct monetary loss, theft of intellectual property, or disruption of operations that affect revenue.
- Regulatory penalties and compliance violations: Organizations that fail to meet data protection requirements (such as GDPR, CCPA, or HIPAA) may face fines, legal action, or mandated corrective measures.
- Loss of customer trust: Customers and partners may lose confidence if their personal or sensitive information is exposed, potentially reducing loyalty, sales, and long-term revenue.
- Reputational damage: Public disclosure of a data breach can harm an organization’s brand, investor confidence, and market position.
- Operational disruption: Responding to a breach often requires intensive internal resources. Forensic investigation, IT remediation, and communications efforts can slow or halt normal business operations.
- Litigation and legal consequences: Exposure of sensitive information can lead to lawsuits from customers, employees, or partners, potentially resulting in significant settlements or judgments.
How to measure data sensitivity
The sensitivity of data isn’t always fixed. What may be considered highly sensitive in one context could be lower risk in another. Sensitivity can depend on who has access, how the data is stored, and what harm could result if it’s exposed.
Understanding this context is crucial for organizations, as it informs security measures, compliance requirements, and risk management strategies.
Two widely used methods for assessing sensitivity are the Confidentiality, Integrity, and Availability (CIA) framework and data classification levels.
Confidentiality, integrity, and availability (CIA)
The National Institute of Standards and Technology (NIST) is a U.S. federal agency that develops standards and guidelines for information security. In the Federal Information Processing Standards (FIPS) 199, it uses three key factors to evaluate the sensitivity of data and categorize information systems based on potential impact:
- Confidentiality: How important is it to prevent unauthorized disclosure? How severe would the impact be if this data were exposed?
- Integrity: How critical is it that the information remains accurate and unaltered? What problems could arise if the data were tampered with or corrupted?
- Availability: How essential is it that this information is reliably accessible? How disruptive would it be if access were denied or delayed?
Data classification levels
Data classification is the process of organizing information into categories based on how sensitive it is and what level of protection it requires. By classifying data, organizations can determine who should have access, what controls should be in place, and how to handle it securely throughout its lifecycle.
Common classification tiers include:
- Public: Information that is intended for general access and whose disclosure poses minimal or no risk. Examples include published reports or press releases.
- Internal/private: Data for internal use that, while not intended to be public, would cause limited harm if disclosed. Examples include internal policies or routine operational documents.
- Confidential: Information that could cause harm to individuals or the organization if exposed. Examples include employee records, customer data, and financial statements.
- Restricted/highly confidential: The most sensitive category, comprising information whose unauthorized disclosure would likely result in serious financial, legal, or reputational harm. Examples include trade secrets, proprietary designs, or strategic business plans.
How to protect sensitive data
For individuals
Even if you don’t manage large datasets or run a business, it’s still important to protect your own sensitive data. The following steps can help keep that data safe and significantly lower the likelihood of identity theft, fraud, or account compromise.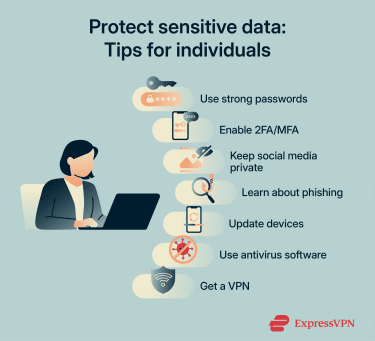
Secure sensitive accounts
Online accounts often serve as gateways to sensitive data, such as financial records, private communications, and other confidential information.
You can strengthen account security by:
- Using strong passwords: A strong password is long and difficult to guess. It should combine uppercase and lowercase letters, numbers, and symbols. Avoid using personal details such as your name or birth date.
- Having unique passwords: Reusing the same password across multiple services means a single breach could expose several accounts.
- Getting a password manager: If you have trouble remembering complex, unique passwords for multiple accounts, a password manager like ExpressKeys can help. These tools securely store your passwords in an encrypted vault and can automatically fill them in when you sign into websites or apps.
- Enabling 2FA or MFA whenever possible: Both of these add an extra layer of protection to your account by requiring another form of verification in addition to your password, such as a one-time code from an authentication app. Even if someone obtains your password, they can’t access your account without the second factor.
Practice online privacy and safety
Sensitive data can be exposed because of risky online habits, such as having unused email accounts, downloading files from shady websites, or oversharing personal information.
Here are some simple steps you can take to reduce your risk:
- Limit who can see your social media profiles: Bad actors can use information gathered from posts for scams or impersonation.
- Remove sensitive data from the internet: Delete old, unused accounts and remove unnecessary personal details from public profiles. A data removal service like Identity Defender (available to U.S. users on select ExpressVPN subscriptions) can also help. Identity Defender’s Data Removal feature locates your personal information on data broker and people-search sites and submits removal requests on your behalf.
- Avoid suspicious links and files: Clicking on links or downloading files from unknown or untrusted sources could expose you to phishing attacks or malicious software.
- Learn to recognize phishing red flags and scam tactics: For example, be extra cautious if a message tries to pressure you into acting immediately by creating urgency.
Lock down devices and networks
It’s important to protect devices and networks against unauthorized access, malware, and other threats that could expose your sensitive data.
You can do this by:
- Keeping software and apps up to date: Install OS and app updates promptly; they often contain patches to security vulnerabilities that attackers could exploit.
- Check and configure firewalls: Ensure your device and network firewalls are active and properly set up to block unauthorized access.
- Secure your home network: Enable Wi-Fi Protected Access 3 (WPA3) encryption if it’s available, disable unused network features, and set up a guest network for visitors.
- Install a reputable antivirus: These tools are designed to detect and block malware that could potentially compromise your data.
- Use a virtual private network (VPN): VPNs encrypt your internet traffic, protecting your online privacy and making it harder for attackers to intercept your data. This is particularly important on public or untrusted Wi-Fi networks, where unsecured connections make it easier for cybercriminals to capture sensitive information like login credentials or financial data.
For organizations
For organizations, protecting sensitive data requires a combination of policies, technical controls, and employee awareness. Here’s how to approach it in practice.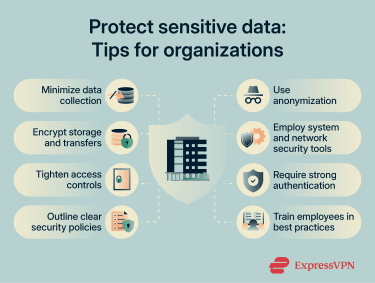
Data minimization and purpose limitation
Data minimization means only collecting the data that’s necessary for your operations or a specific task. Purpose limitation means using that data solely for the purpose for which it was collected. By applying both principles, organizations decrease their attack surface, reducing the likelihood of misuse or a breach.
Data masking
When sensitive data needs to be used for things like testing systems, running reports, or analyzing trends, techniques like anonymization and pseudonymization can help protect it.
Anonymization removes or alters personal details so that individuals can’t be identified at all. Pseudonymization replaces personal details with codes (e.g., a name replaced by a unique ID number). The real identities are kept separately and can only be linked to the code under controlled conditions.
Secure storage
Keep sensitive data safe while it’s stored by using encryption. Encryption converts data into a code that can’t be read without the right key.
Organizations should also use monitoring tools and data loss prevention (DLP) systems. These track how data is being accessed and detect unusual activity that could indicate a risk, including attempts at data exfiltration.
Finally, data that’s no longer needed should be securely disposed of to reduce the risk of compromise.
Safe sharing
When sensitive data must be shared with colleagues or trusted partners, end-to-end encryption ensures that only the sender and intended recipient can read the information.
Organizations should also implement access control, applying the principle of least privilege and giving individuals access only to the data they need to do their job. Techniques such as just-in-time access can be used to further reduce risk by granting temporary permissions only when needed, automatically revoking them afterward.
Finally, strong authentication methods, such as MFA, should be implemented to verify that anyone accessing the data is who they claim to be.
Employee training and security policies
Human error is a common factor in data incidents. For example, employees might fall for a phishing email or have their account compromised due to a weak password. These mistakes can lead to data exposure or unauthorized access.
That’s why regular employee training is important. It helps staff understand how to handle sensitive data safely and follow proper procedures for sharing, storing, and disposing of information. They can also be taught how to recognize phishing or social engineering attempts.
Training should be reinforced by clear security policies with rules for accessing, using, and protecting sensitive data. Policies should also include guidance on devices, remote work, and third-party services. Together, these help strengthen the organization’s overall security posture.
Learn more: How to prevent a data breach
What to do after a data breach
If your organization suspects a data breach, it’s important to immediately report the incident to your technical or security team. Below are other common actions companies usually take to limit harm and begin recovery.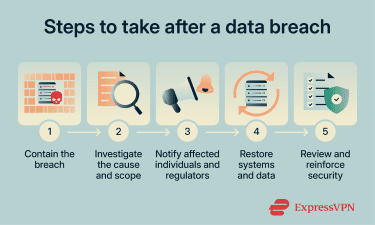
Containment and investigation steps
The priority is to contain the breach. This may involve isolating affected systems, changing passwords, and restricting network access. Organizations should then investigate to determine what data was accessed, how the breach occurred, and who or what was involved.
Steps taken are always documented. It’s important to keep logs for internal review, understanding the scope of the incident, and supporting any regulatory or legal reporting obligations.
Notification and reporting requirements
Depending on the type of data and the jurisdiction, organizations may be required to notify affected individuals, regulators, or partners. Even when not legally mandated, prompt notification can help limit harm and maintain trust.
Communications should clearly explain what happened, what data may have been exposed, and steps recipients can take to protect themselves. Internally, reporting ensures leadership and technical teams can coordinate the response effectively.
Recovery and long-term improvements
After containment, organizations should restore systems and data from secure backups and reinforce security measures to prevent repeat incidents. Reviewing policies, procedures, and technology can help identify gaps, strengthen overall security posture, and guide future employee training.
Data privacy regulations
Legal obligations for data privacy depend on factors such as where an organization operates, what kinds of data it handles, and who its customers are.
General Data Protection Regulation (GDPR)
The GDPR is a data protection law that governs the processing of personal data of individuals in the EU and the European Economic Area (EEA). It applies to organizations inside and outside these regions that offer goods or services to, or monitor the behavior of, EU and EEA residents.
GDPR defines rights for individuals, such as access, correction, and deletion of special categories of personal data. It requires organizations to establish legal bases for processing, implement safeguards, and report breaches.
California Consumer Privacy Act (CCPA)
The CCPA gives California residents specific rights over their personal information and imposes obligations on certain businesses. It applies to for‑profit entities that do business in California and meet revenue or data processing thresholds.
Under the CCPA, consumers can request disclosure of the data collected about them, request deletion, and opt out of the sale of their personal information.
California Privacy Rights Act (CPRA)
The CPRA expands and amends the CCPA, adding new consumer rights and stronger protections for sensitive personal information. It established the California Privacy Protection Agency to enforce compliance, clarifies definitions, and introduces risk‑based data minimization and retention requirements.
New York SHIELD Act
The New York Stop Hacks and Improve Electronic Data Security (SHIELD) Act strengthens data security and breach notification obligations for businesses handling private information of New York residents.
It broadens the definition of private information, expands what constitutes a breach to include unauthorized access, and requires reasonable administrative, technical, and physical safeguards.
The SHIELD Act applies to any business that owns or licenses computerized data of New York residents, regardless of where the business is located.
Health Insurance Portability and Accountability Act (HIPAA)
HIPAA is a U.S. federal law that sets standards for safeguarding PHI. It applies to “covered entities” (healthcare providers, health plans, and healthcare clearinghouses) and their business associates.
HIPAA requires the implementation of administrative, physical, and technical safeguards for PHI, including breach notification requirements.
Gramm-Leach-Bliley Act (GLBA)
The GLBA is a U.S. federal law that mandates financial institutions to protect the privacy and security of consumers’ nonpublic personal information. It requires clear disclosures and certain opt‑out options, and it requires institutions to design, implement, and maintain safeguards to protect customer information.
Payment Card Industry Data Security Standard (PCI DSS)
The PCI DSS is a set of security requirements developed by the PCI Security Standards Council for organizations that store, process, or transmit payment card data. It’s not a federal law, but compliance is contractually required by major payment brands.
PCI DSS provides technical and operational controls to protect cardholder data and mitigate fraud risk. Anonymization permanently removes identifiable details so individuals can’t be recognized. Pseudonymization replaces personal identifiers with codes that can only be reversed under controlled conditions.
FAQ: Common questions about sensitive data
What are examples of sensitive data?
What is data sensitivity?
What is the difference between sensitive data and personal data?
How do regulations like GDPR address sensitive data?
What is data masking?
What are anonymization and pseudonymization?
What is data loss prevention?
How long should sensitive data be retained?
What should I do if my sensitive data is exposed?
Take the first step to protect yourself online. Try ExpressVPN risk-free.
Get ExpressVPN